Networking
- For local dev/testing, networks usually "just works"
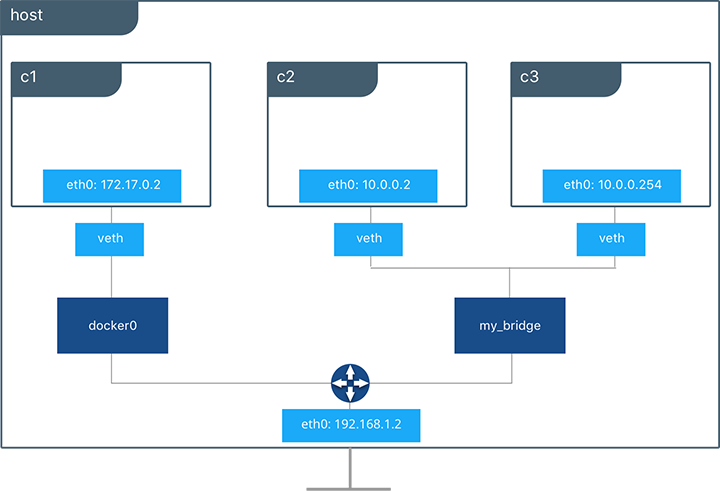
- Each container by default connected to a private virtual network "bridge"
- Each virtual network routes through NAT firewall on host IP
- All containers on a virtual network can talk to each other without -p
- Best practice is to create a new virtual network for each app:
network "my_web_app"for mysql and php/apache containersnetwork "my_api"for mongo and nodejs containers
- "Batteries Included, But Removable"
- Defaults work well in many cases, but easy to swap out parts to customize it
Default Security
- Create your apps so frontend/backend sit on same Docker network
- Their inter-communication never leaves host
- All externally exposed ports closed by default
- Must be manually exposed by
-p, which is better default security!
DNS
- FORGET IP's
- Static IP's and using IP's for talking to containers is an anti-pattern. Should be avoided!
- Docker daemon has built-in DNS server that containers use by default
Defaults the hostname to the container's name, but can also be set an aliases
Containers shouldn't rely on IP's for inter-communication
DNS for friendly names is built-in if you use custom networks
Docker Compose makes it easier to manage DNS
Several Networking diagrams